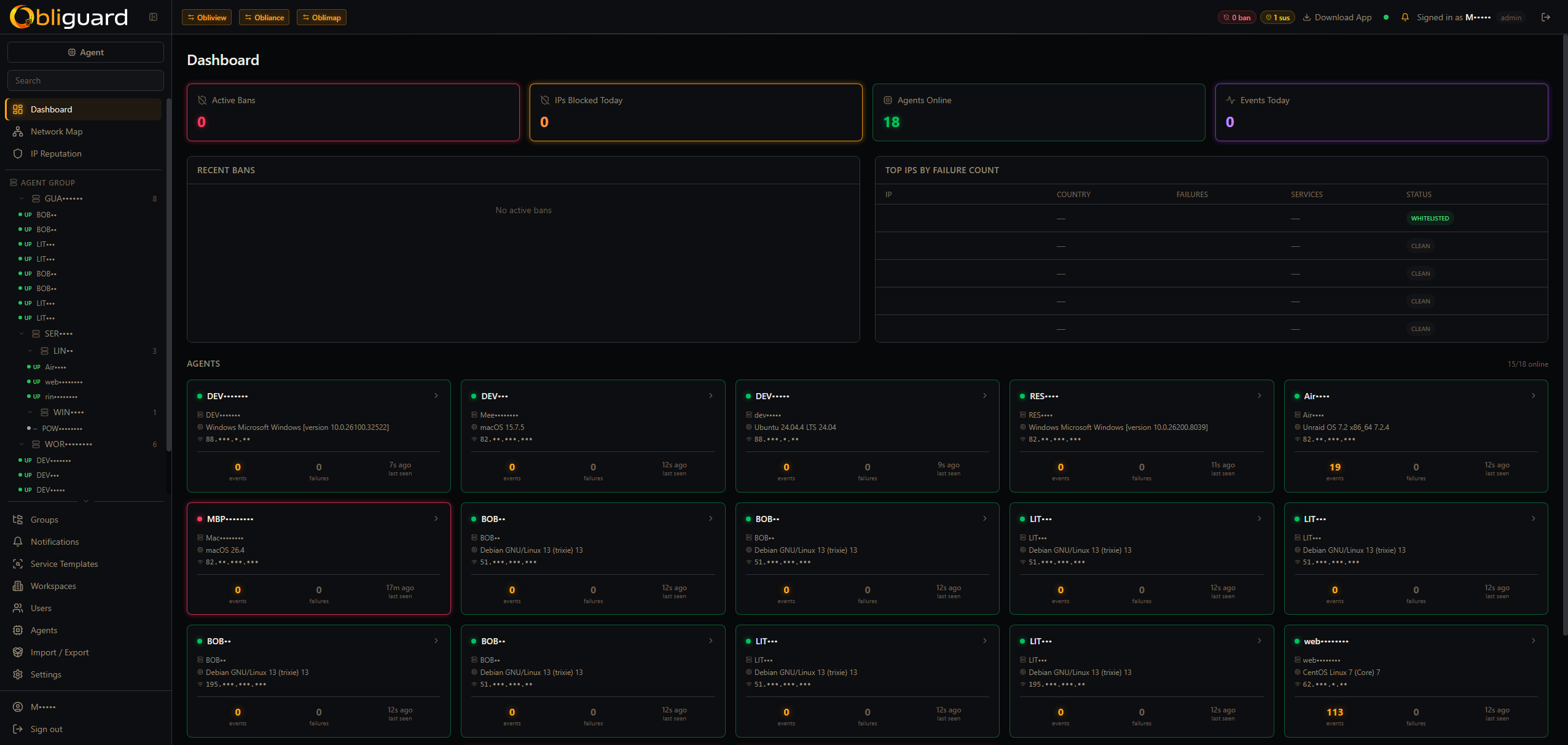
How it works
Logs in, bans out — across every machine
Configure which services to watch on each machine. Agents tail logs (and Windows Event Log for RDP) and stream events to the central server, which analyses, scores and enforces bans automatically across your entire infrastructure.
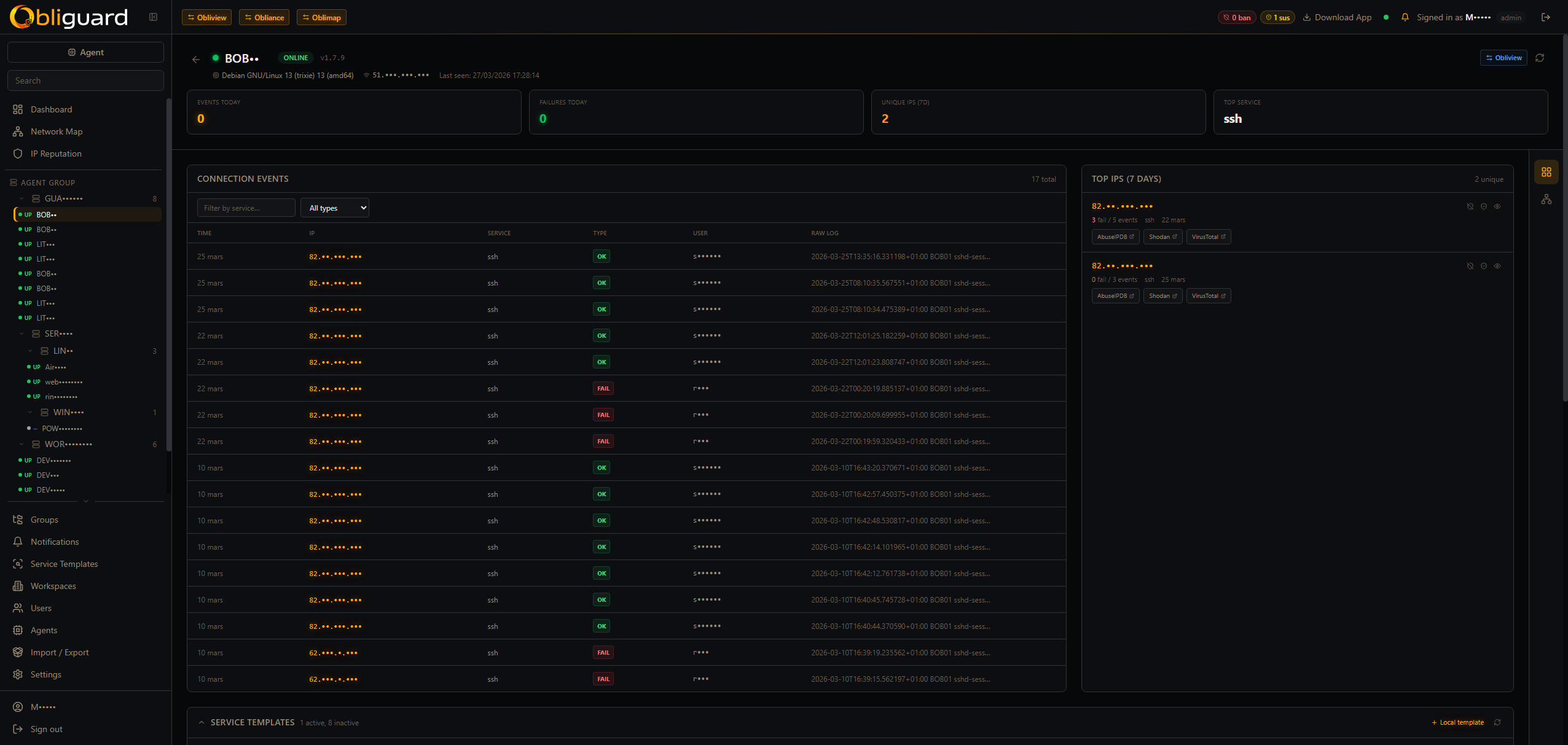
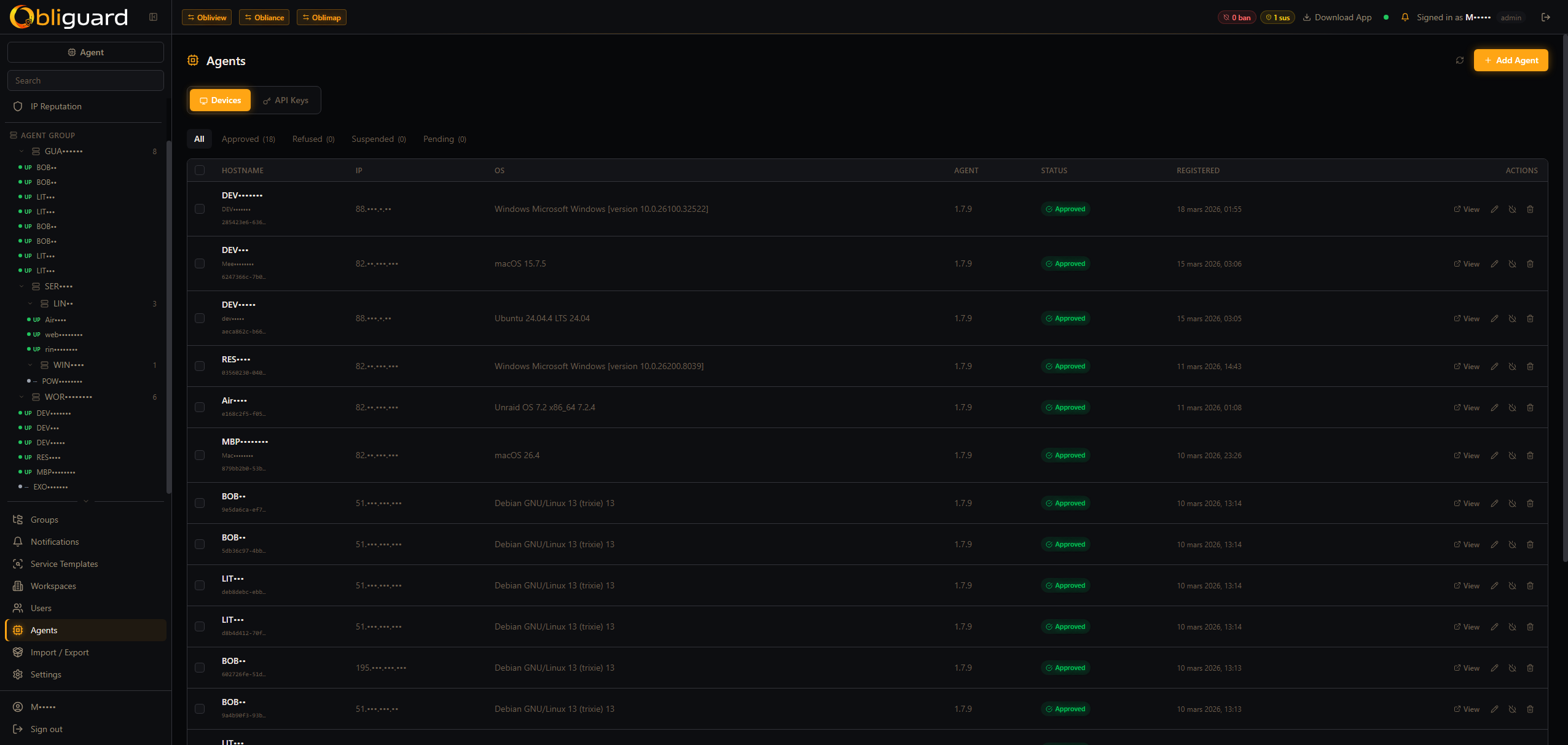
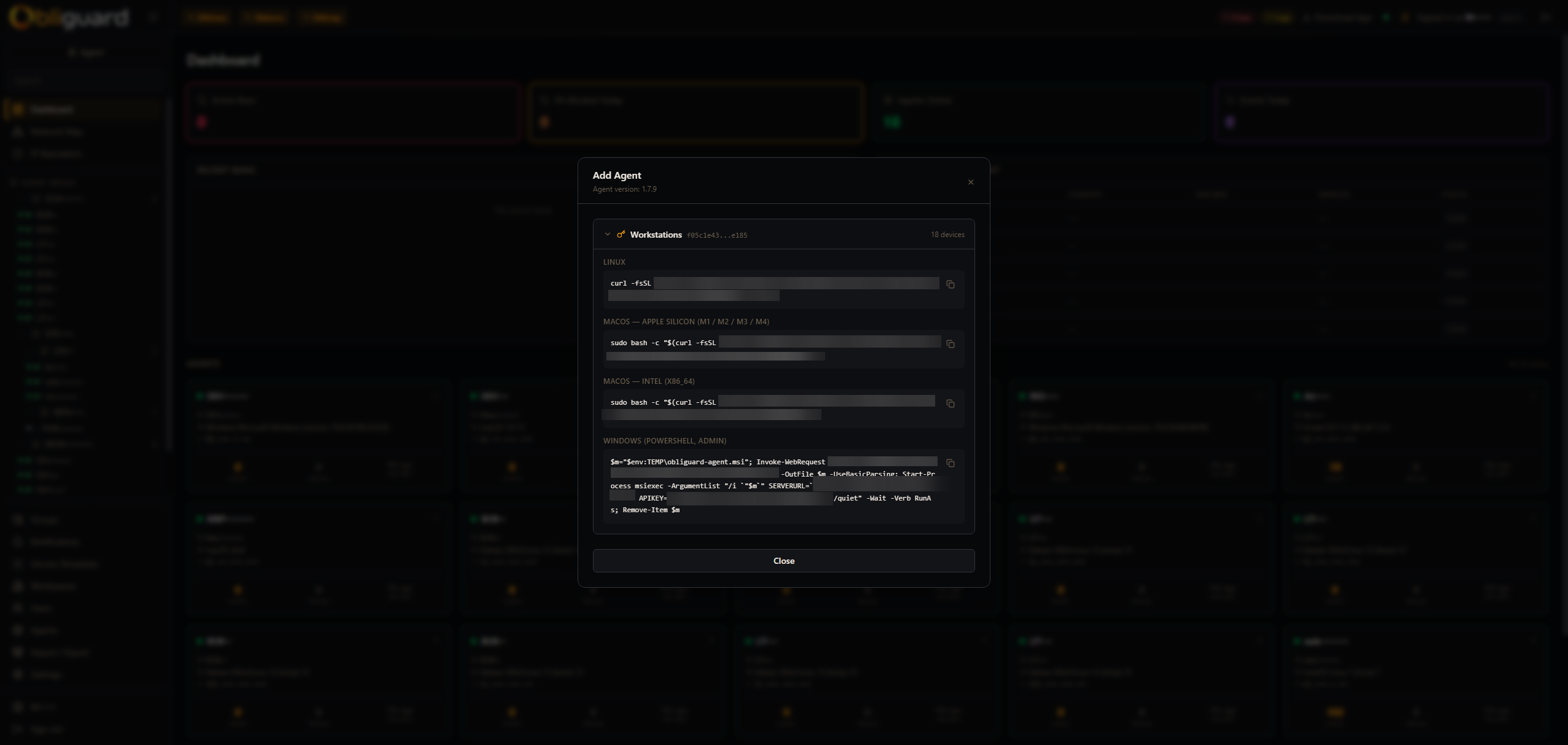
Log collection agents
Lightweight agents run on each machine, tailing service logs and Windows Event Log (EventID 4625/4624 for RDP). Zero inbound ports required; agents push to the central server.
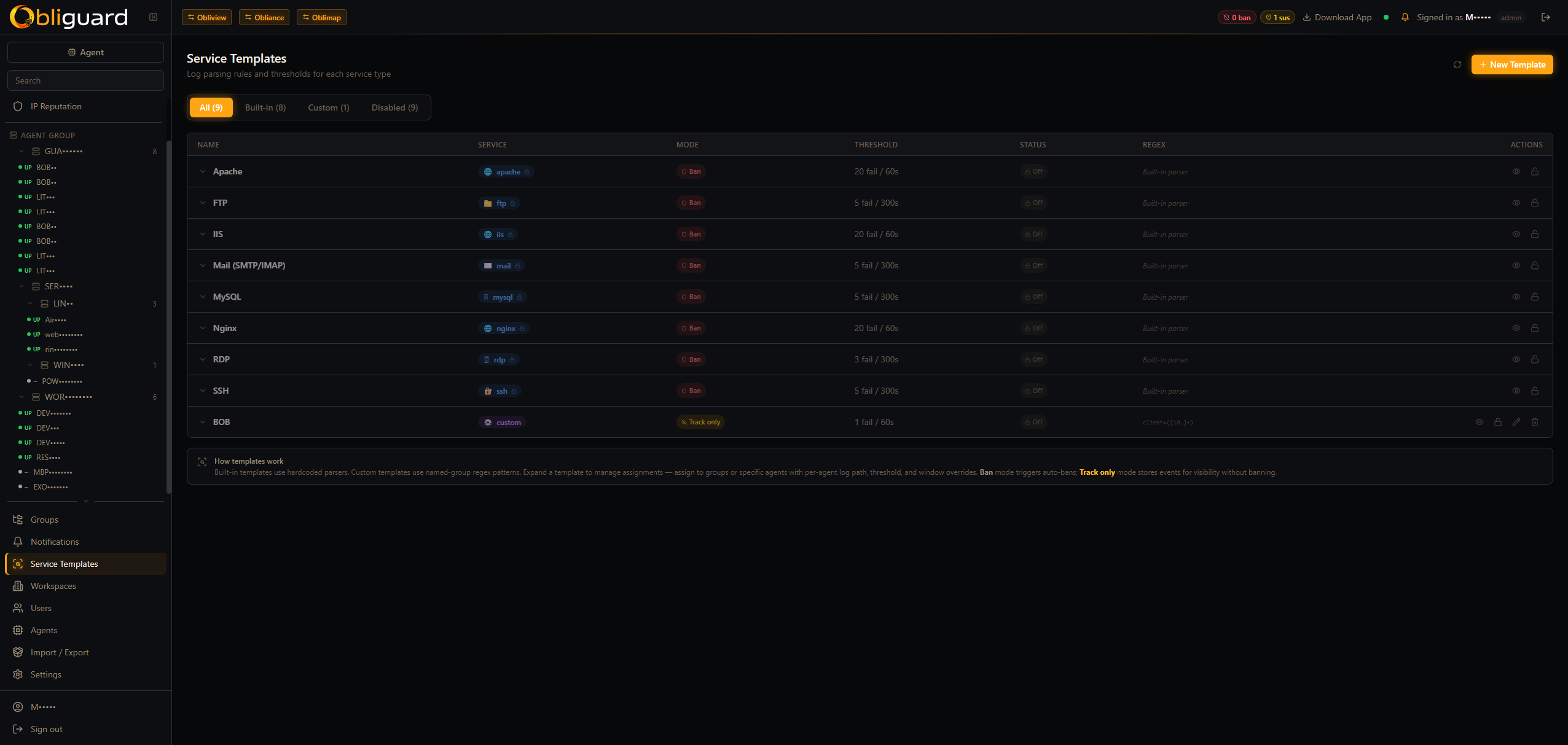
Ban engine — 30-second evaluation cycle
The central server parses events on a 30-second cycle and assigns threat scores. Auth failures accumulate within configurable time windows — escalating from clean to suspicious to banned. Service templates define custom regex, threshold, time window and mode (ban or track).
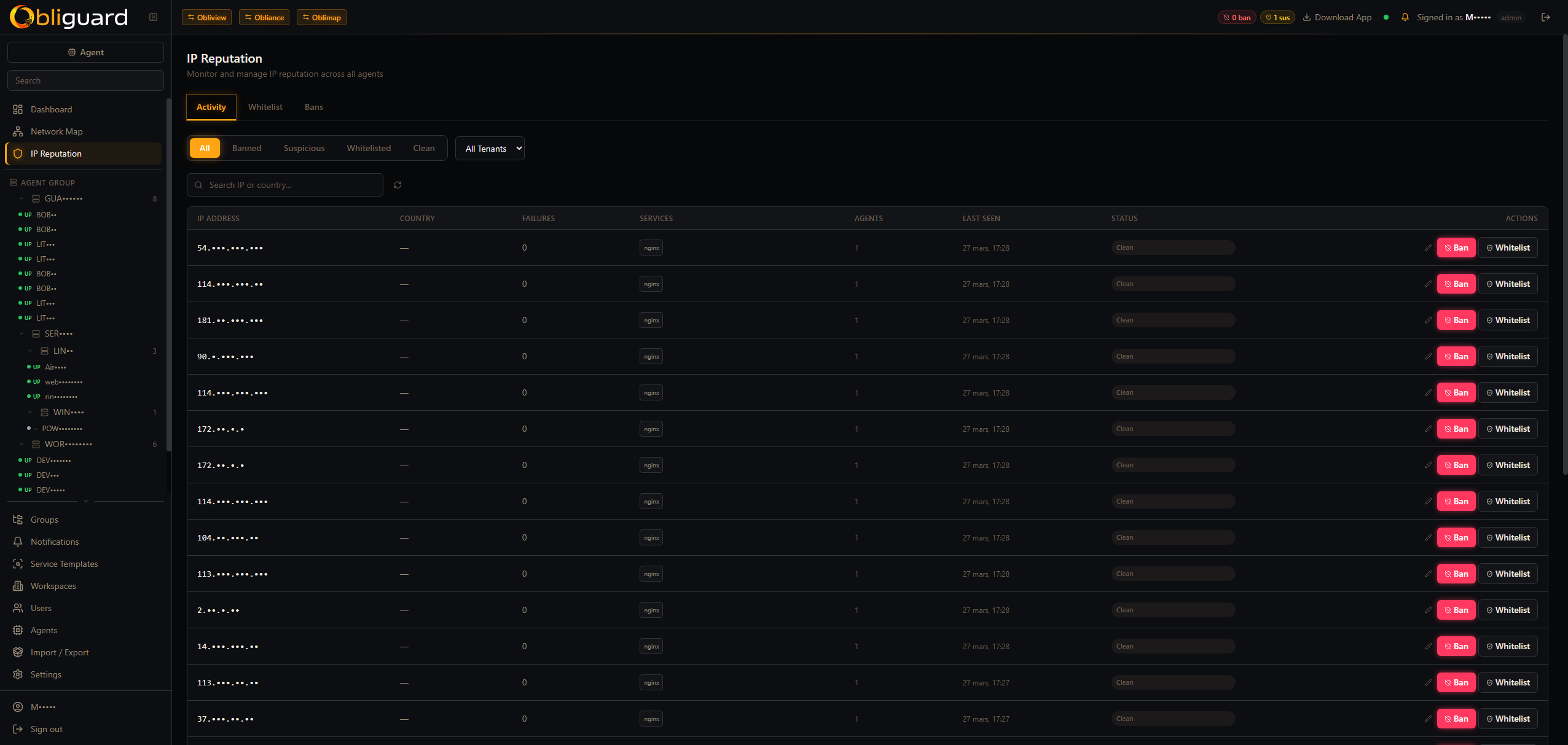
Scoped bans with optional TTL
Bans are scoped to global / tenant / group / agent. Auto-bans are created by the engine; admins can also create manual bans. Optional TTL triggers auto-deactivation when the window expires. Whitelisted IPs (CIDR notation) are never auto-banned.
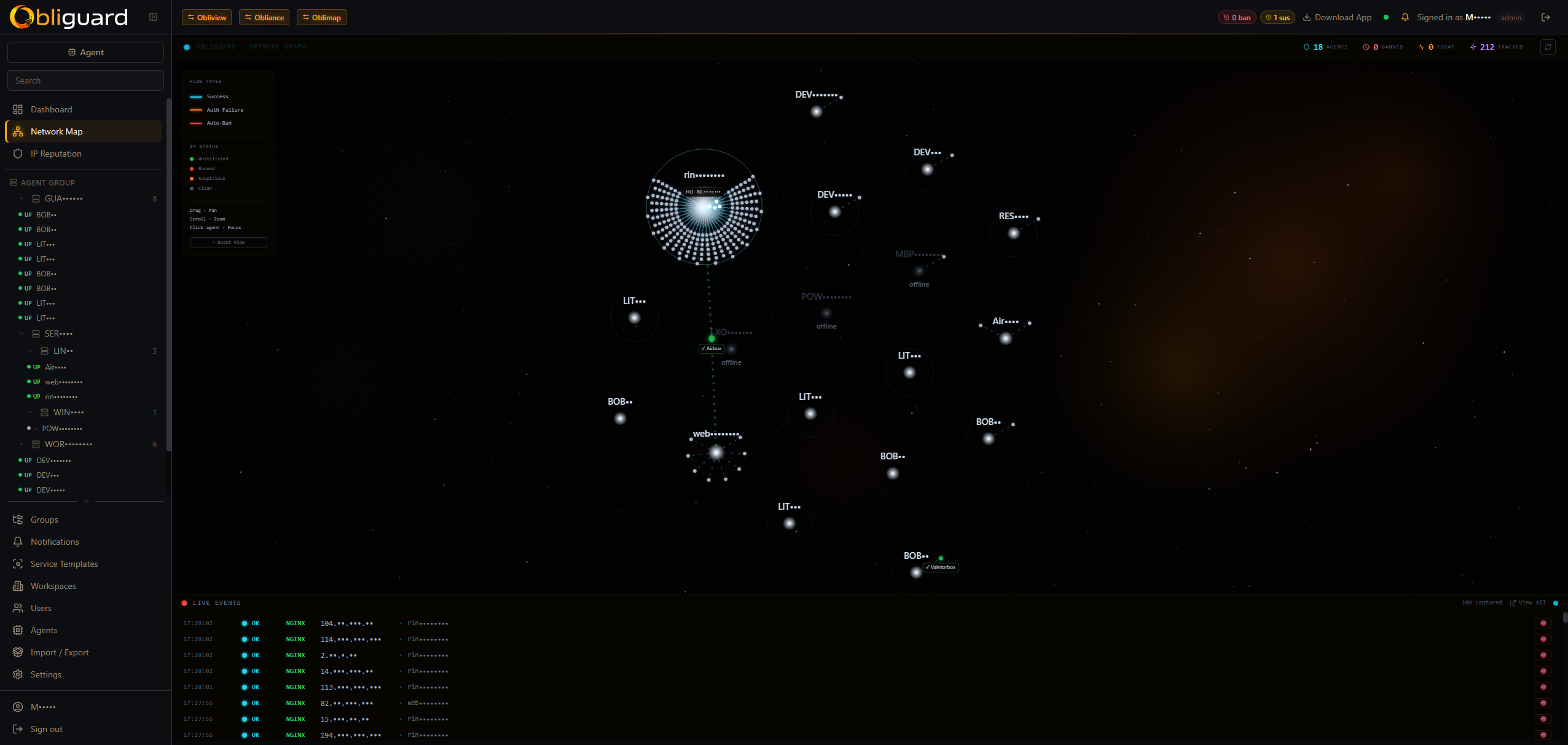
NetMap — live network canvas
Canvas 2D visualisation of agents, IPs, peer links, live particles and ripples — with country flags and GeoIP data (country, city, ASN). Click any IP node to see its full history: failure/success counts, affected agents, usernames attempted, reputation status.
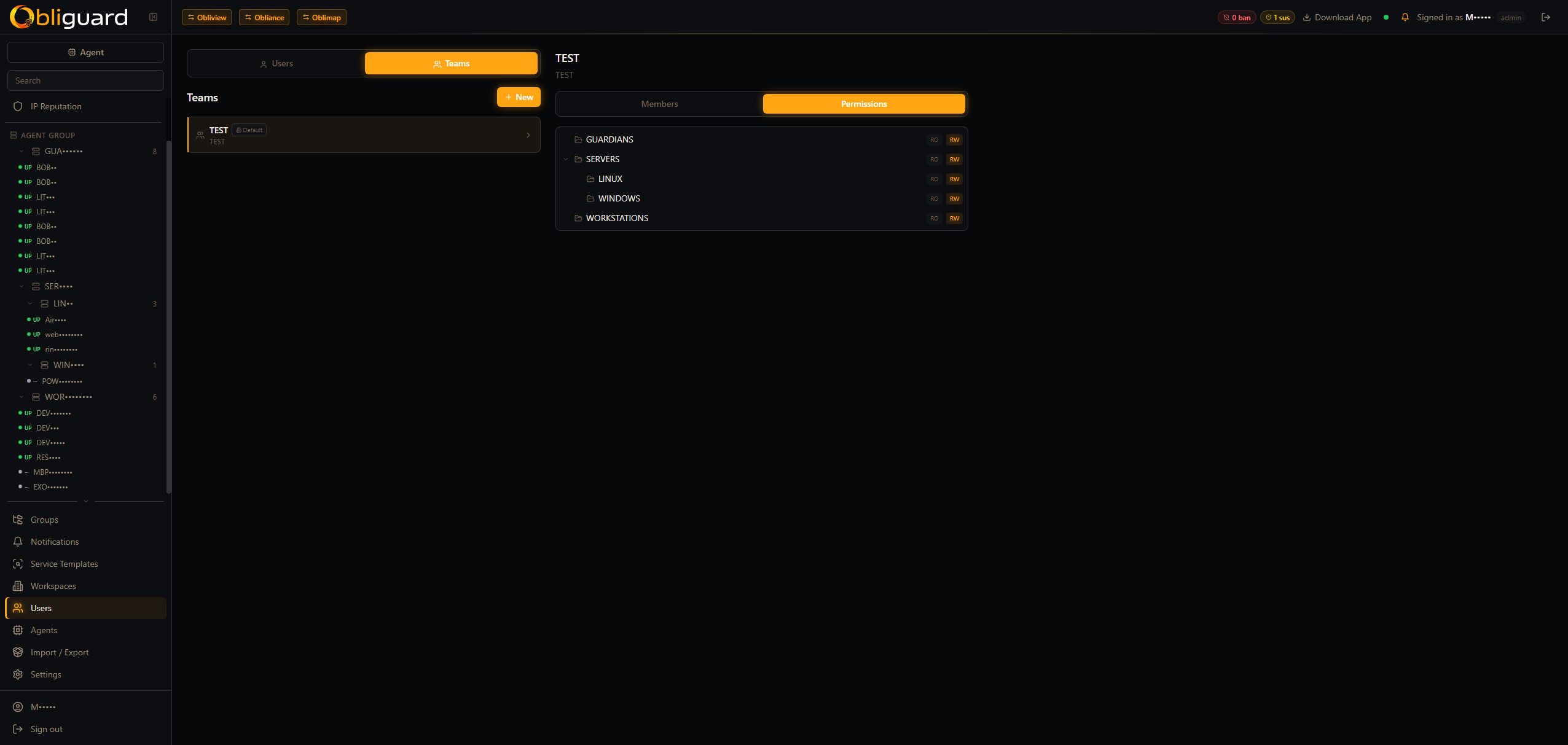
Agent groups
Group machines by role or environment and apply a shared service profile to the entire group at once. A web cluster, a DB cluster, an edge tier — each gets exactly the services it needs.
IP reputation & GeoIP
Every IP carries a reputation status — clean → suspicious → banned — enriched with GeoIP data (country, city, ASN). Track failure/success counts, which agents were hit, and which usernames were attempted.
Multi-tenant for MSPs
Deploy one Obliguard instance for your entire client base. Each tenant has isolated data, their own console and their own agent fleet. Tenant-level exemptions (ip_ban_exclusions) let you whitelist trusted IPs per customer.
Real-time flow analyser
Planned — deep packet-level traffic analysis. Pending kernel driver development. Will extend the star map with full flow visibility.